Blog
Back to blog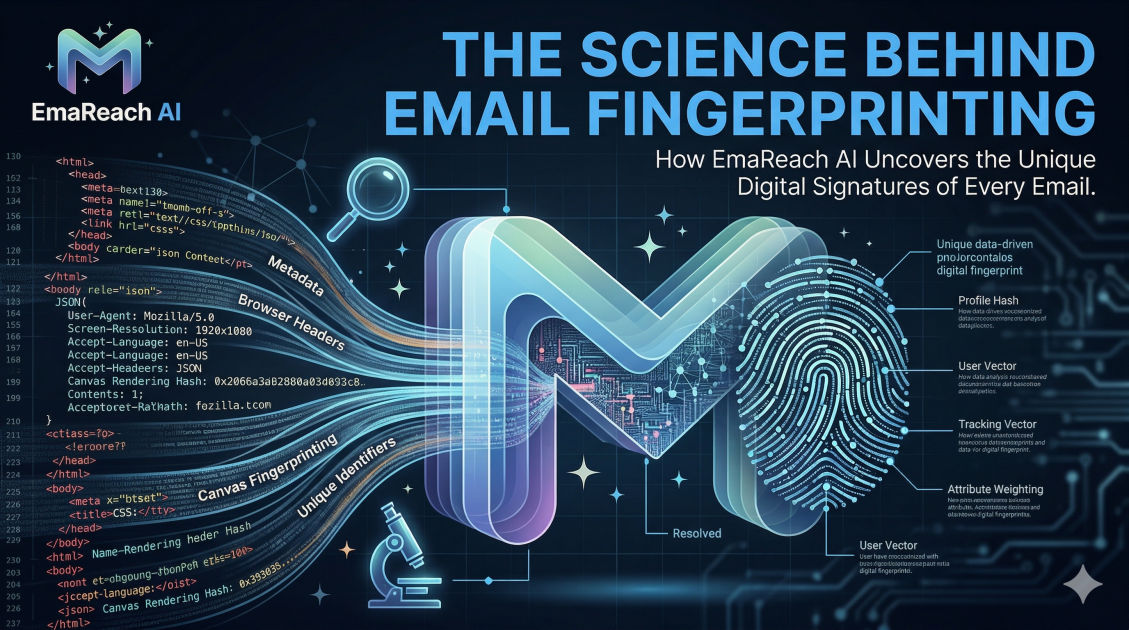
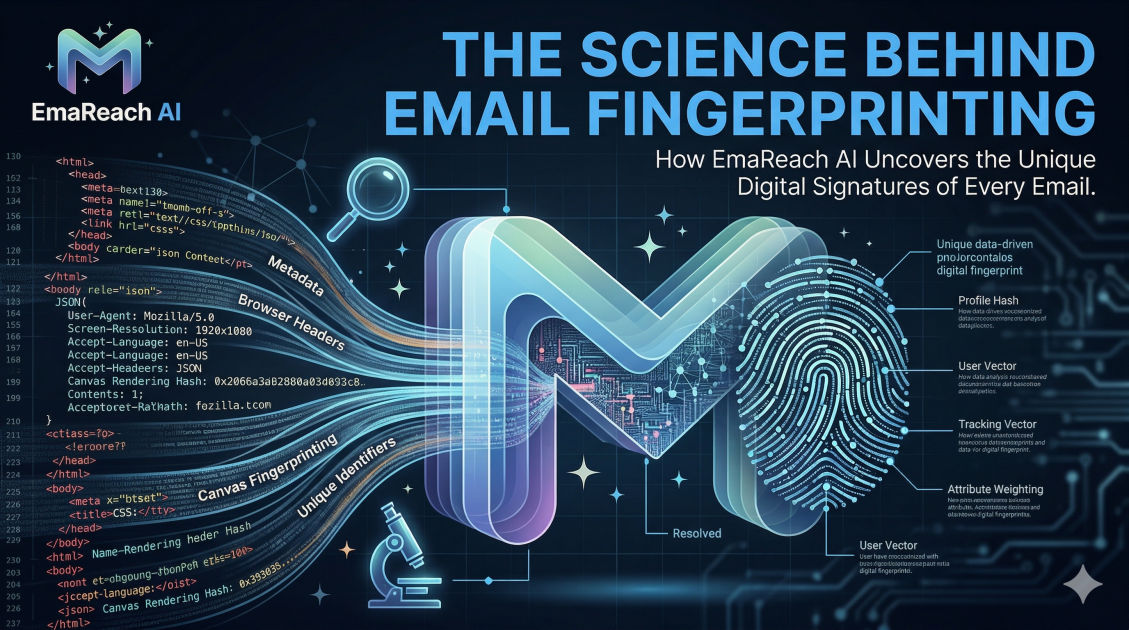
The Science Behind Email Fingerprinting
email deliverabilityemail fingerprintingcold outreachspam filtersemail marketingtechnical seo
Introduction to Email Fingerprinting
In the modern digital landscape, the journey of an email from a sender's outbox to a recipient's inbox is far more complex than it appears. Behind the scenes, sophisticated algorithms and security protocols work tirelessly to filter through billions of messages. One of the most advanced and least understood mechanisms in this process is email fingerprinting. This scientific approach to identification allows Mail Transfer Agents (MTAs) and Internet Service Providers (ISPs) to recognize, categorize, and often block content based on unique digital signatures that go far beyond simple keyword filtering.
Email fingerprinting is a technique used by anti-spam systems to identify and track messages by creating a unique 'hash' or digital shorthand of the email's characteristics. When a sender broadcasts a high volume of identical or near-identical messages, fingerprinting allows receiving servers to spot the pattern instantly. Understanding the science behind this process is essential for any professional involved in high-volume outreach or digital communication.
The Anatomy of a Digital Fingerprint
A digital fingerprint is not a single data point but a composite score derived from various elements of an email's structure and content. To understand how these are formed, we must look at the mathematical underpinnings of hashing algorithms.
Hashing Algorithms and Checksums
At its core, fingerprinting relies on cryptographic hash functions. A hash function takes an input (like the body of your email) and produces a fixed-size string of characters, which is typically a hexadecimal number. The primary characteristic of a good hash function is that even a tiny change in the input—such as changing a single comma to a period—will result in a completely different hash.
ISPs use these hashes to create 'fuzzy' signatures. Unlike a standard hash that requires an exact match, fuzzy hashes are designed to detect similarity. This means that if you try to bypass filters by changing a few words in each email, the fuzzy fingerprint will still identify the messages as being part of the same campaign.
Structural Analysis
Fingerprinting also examines the 'skeleton' of an email. This includes:
- MIME Parts: The way the Multi-Purpose Internet Mail Extensions are structured.
- HTML Hierarchy: The specific nesting of tags (e.g.,
<div>within<table>). - Header Ordering: The sequence in which headers like
Subject,From, andMessage-IDappear. - CSS Patterns: Inline styles and classes used within the HTML body.
By analyzing these structural elements, an ISP can identify the specific software or 'sending engine' used to generate the email, even if the content itself varies.
How ISPs Use Fingerprinting to Combat Spam
ISPs maintain massive databases of known spam fingerprints. When an incoming email arrives, the server quickly generates a fingerprint and compares it against these databases. This happens in milliseconds.
The Role of Real-time Blackhole Lists (RBLs)
Many fingerprinting systems are collaborative. Organizations like Spamhaus or Cloudmark collect fingerprints from 'honeypots' (trap email addresses) and distribute them globally. If your email's fingerprint matches a known malicious signature in these repositories, your message is blocked before it even hits the spam folder.
Reputational Scoring
Fingerprinting is also tied to sender reputation. If a specific fingerprint is consistently associated with high complaint rates or low engagement, the ISP will assign a 'negative weight' to that signature. Over time, any email bearing a similar fingerprint will face stricter scrutiny, regardless of the IP address or domain it is sent from.
The Technical Components of an Email Signature
To truly grasp the science, we must dissect the specific components that contribute to an email's unique identifier.
Content-Based Fingerprinting
This focuses on the semantic and syntactic patterns within the message. Algorithms analyze the ratio of text to images, the frequency of certain 'trigger' words, and the presence of suspicious links. More advanced systems use Natural Language Processing (NLP) to understand the intent of the message. If the intent matches the profile of a phishing attempt or a low-quality mass solicitation, the fingerprint is flagged.
Metadata and Header Fingerprinting
Every email contains metadata that acts as a digital trail. The X-Mailer header, for example, identifies the software used. If a sender claims to be sending from a personal Gmail account but the header reveals a bulk-sending script, the discrepancy creates a high-risk fingerprint. Furthermore, the routing information—the 'Received' headers—shows every server the email passed through. Patterns in this routing can be fingerprinted to identify botnets or unauthorized relays.
The Challenge of Content Variation
For legitimate marketers, the goal is to avoid having their messages misidentified as spam. Many attempt to use 'spintax' or dynamic tags to vary their content. While this can help, modern fingerprinting is designed to see through these tactics.
Fuzzy Matching Logic
Fuzzy hashing algorithms, such as SSDEEP or Nilsimsa, are specifically designed to detect content that is 'mostly similar.' These algorithms break the text into small 'shingles' or chunks and hash each chunk. The final fingerprint is a collection of these hashes. If two emails share 80% of the same shingles, they are considered a match. This is why simple personalization (like adding a name or company) is often insufficient to break a fingerprint.
Image Fingerprinting
Spammers often try to hide text within images to evade text-based filters. In response, ISPs have developed image fingerprinting. This involves analyzing the pixel density, color histograms, and metadata of images. Even if an image is slightly resized or cropped, the fingerprinting algorithm can often recognize it as the same visual asset used in a known spam campaign.
The Impact on Email Deliverability
If your emails are being fingerprinted as 'bulk' or 'promotional,' they are likely to be diverted to the Promotions tab or, worse, the Spam folder. This is a critical issue for B2B outreach where landing in the Primary tab is essential for success.
When your fingerprints are flagged, you may experience:
- Throttling: The ISP limits how many emails you can send per hour.
- Soft Bounces: Temporary rejections with codes indicating 'reputation issues.'
- Greylisting: The server temporarily rejects the email and asks the sender to try again later, a test that many automated spam scripts fail.
To ensure your communications are not sidelined by these technical hurdles, you need a system that understands and mitigates the risks of fingerprinting. Stop Landing in Spam. Cold Emails That Reach the Inbox. EmaReach (https://www.emareach.com/) is specifically designed to navigate these complexities. EmaReach AI combines AI-written cold outreach with inbox warm-up and multi-account sending—so your emails land in the primary tab and get replies. By diversifying the technical footprint of your campaigns, EmaReach helps you stay ahead of aggressive fingerprinting algorithms.
Advanced Fingerprinting: Machine Learning and AI
The science of fingerprinting is evolving. We are moving away from static rules and toward dynamic, machine-learning-based models. These models don't just look for a specific hash; they look for 'behavioral fingerprints.'
Behavioral Analysis
A behavioral fingerprint tracks the patterns of a sender over time. This includes:
- Sending Velocity: How quickly are emails being sent?
- Volume Spikes: Does the sender suddenly go from 0 to 10,000 emails a day?
- Engagement Ratios: What percentage of recipients are opening, clicking, or reporting the email?
If your 'behavior' matches the profile of a spammer, your fingerprint becomes toxic. This is why 'warm-up' periods are so critical. They allow you to build a positive behavioral fingerprint before scaling your outreach.
Strategies to Manage Your Email Fingerprint
While you cannot prevent an ISP from fingerprinting your emails, you can ensure that the fingerprint generated is viewed as 'clean' and 'legitimate.'
1. Technical Alignment (SPF, DKIM, DMARC)
Authentication protocols like SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance) are the foundation of a healthy fingerprint. They prove that the email is actually from who it says it's from. An unauthenticated email creates a 'suspicious' fingerprint immediately.
2. Infrastructure Diversification
Sending all your emails from a single IP address or a single domain makes it very easy for ISPs to build a comprehensive fingerprint of your activity. By spreading your sending volume across multiple authenticated accounts and domains, you dilute the 'bulk' signature. This is a core feature of platforms like EmaReach, which automates this multi-account strategy to protect your sender reputation.
3. Deep Personalization
Go beyond {{FirstName}}. To break fuzzy hashes, you need significant variation in the body of the email. This can include referencing specific articles the recipient wrote, mentioning their specific job responsibilities, or providing a unique insight relevant only to their company. The more unique the text, the harder it is for a fingerprinting algorithm to cluster your messages.
4. Clean Code and Minimalist Design
Avoid 'dirty' HTML. Excessive use of tracking pixels, nested tables, and complex CSS can create a 'heavy' structural fingerprint associated with commercial marketing templates. Keep your outreach emails as close to 'plain text' as possible. This mimics the fingerprint of a standard 1-to-1 email sent from a human-operated client like Outlook or Gmail.
The Role of Inbox Warm-up
One of the most effective ways to influence your fingerprint's reputation is through automated inbox warm-up. This process involves sending a low volume of emails to 'friendly' accounts that interact with the messages (opening them, moving them to primary, marking them as important).
These positive interactions are recorded by ISPs and associated with your sending fingerprint. Over time, this builds 'social proof' for your email signature. When you eventually send your actual outreach, the ISP recognizes the fingerprint as one that historically generates high engagement, significantly increasing your chances of reaching the primary inbox.
Monitoring and Adapting to Fingerprint Flags
Fingerprinting is not a 'set it and forget it' problem. It requires constant monitoring. Professionals use tools like Google Postmaster Tools to track how their domain is being perceived by major ISPs. If you notice a sudden drop in deliverability despite no changes in your content, it is a strong signal that your current fingerprint has been flagged.
In such cases, you must adapt. This might involve:
- Changing your email templates entirely to reset the structural fingerprint.
- Rotating your sending domains.
- Pausing outreach to focus on a 're-warming' phase.
Conclusion: The Future of Email Science
Email fingerprinting represents the pinnacle of the ongoing battle between senders and filters. It is a sophisticated, mathematically-driven science that relies on structural analysis, fuzzy hashing, and behavioral tracking. As AI continues to advance, we can expect fingerprinting algorithms to become even more adept at identifying intent and context.
For those who rely on email to grow their business, understanding these mechanics is no longer optional. By focusing on technical alignment, content uniqueness, and infrastructure health, you can ensure that your digital fingerprint opens doors rather than closing them. Using advanced tools like EmaReach ensures that your strategy accounts for these scientific realities, combining AI-driven personalization with the infrastructure needed to maintain a pristine reputation.
In the end, the goal of fingerprinting is to ensure that users receive content that is relevant and trustworthy. By aligning your outreach practices with the principles of quality and authenticity, you turn the science of fingerprinting from a hurdle into a competitive advantage.
EmaReach AI
Ready to scale your cold email outreach?
Join thousands of teams using EmaReach AI for AI-powered campaigns, domain warmup, and 95%+ deliverability. Start free — no credit card required.
Related posts
- Read article
The Instantly Alternative That Finally Gets Outbound Analytics Right
Discover why high-volume cold email requires a shift from surface-level vanity metrics to deep, data-driven revenue attribution, and explore the ultimate alternatives for mastering outbound engineering.
- Read article
What You Gain and What You Give Up When Switching From Instantly
Thinking about migrating your cold email stack? This detailed guide breaks down the exact operational advantages you gain and the core features you sacrifice when switching away from Instantly's popular outreach platform.