Blog
Back to blog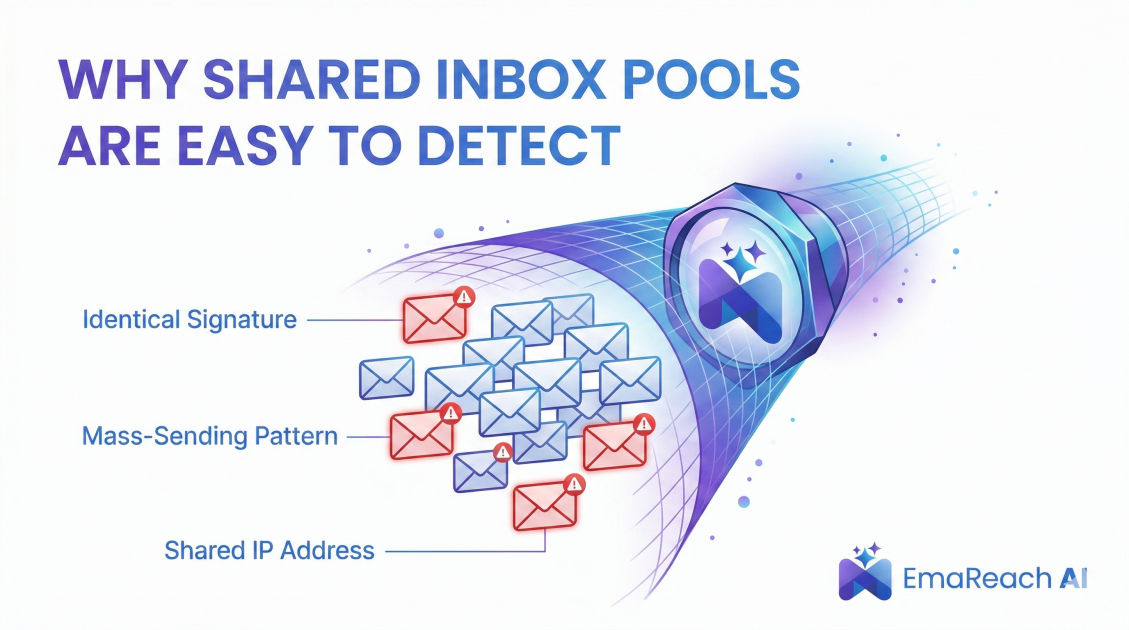
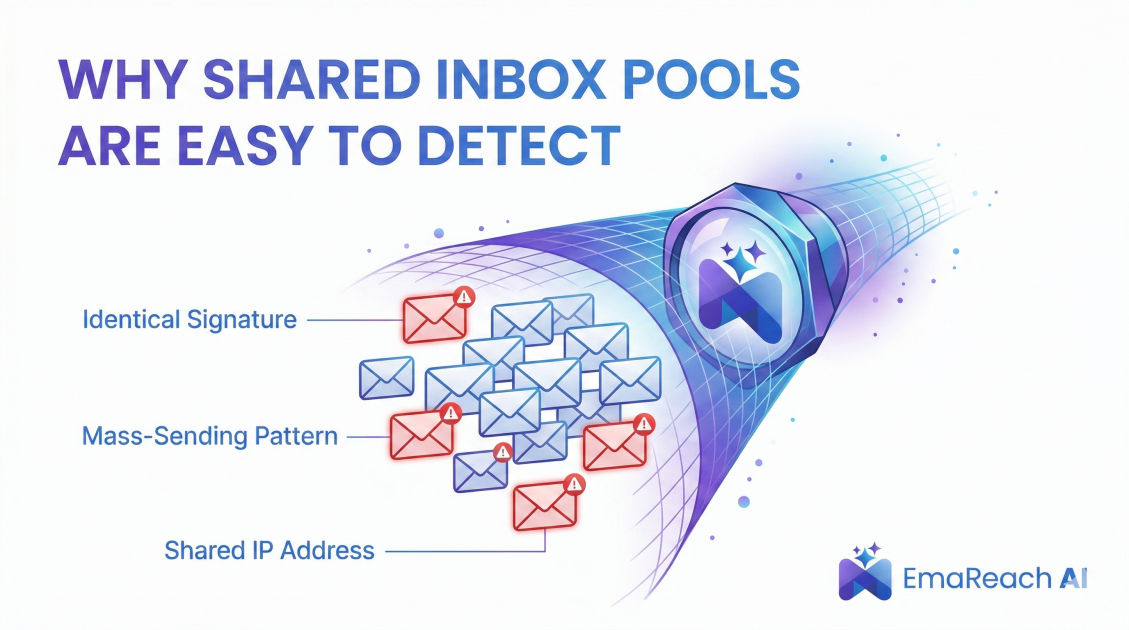
Why Shared Inbox Pools Are Easy to Detect
cold emailemail deliverabilityinbox warm-upspam filtersoutreach strategysender reputation
Introduction
In the high-stakes world of cold outreach and digital communication, deliverability is the invisible foundation upon which every successful campaign is built. For years, marketers and sales professionals have sought shortcuts to bypass the rigorous process of building sender reputation. One of the most common shortcuts is the use of shared inbox pools—large clusters of email accounts used by multiple users to 'warm up' domains or send high volumes of mail. While these pools promise a quick path to the primary inbox, the reality is far more complex.
Modern Mail Transfer Agents (MTAs) and spam filters have evolved into sophisticated gatekeepers. They no longer just look for keywords like 'free' or 'buy now'; they analyze the behavioral DNA of every sender. Shared inbox pools, by their very nature, exhibit distinct patterns that make them incredibly easy for Google, Microsoft, and other major providers to detect and flag. When these pools are identified, the consequences for a sender’s domain reputation can be catastrophic.
Understanding why these pools are so transparent to filters is essential for any professional serious about long-term outreach success. To maintain a competitive edge, many are turning to advanced solutions like EmaReach: Stop Landing in Spam. Cold Emails That Reach the Inbox. EmaReach AI combines AI-written cold outreach with inbox warm-up and multi-account sending—so your emails land in the primary tab and get replies.
The Architecture of a Shared Inbox Pool
A shared inbox pool is essentially a massive network of interconnected email accounts. These accounts are often hosted on the same infrastructure or utilize similar configurations to automate interactions between one another. The goal is to simulate 'engagement'—opening emails, marking them as important, and replying—to trick spam filters into believing the accounts are managed by real humans.
However, this architecture is inherently flawed because it relies on artificiality. Real human communication is messy, sporadic, and diverse. Shared pools are systematic, repetitive, and concentrated. This fundamental difference is the primary signal that modern algorithms exploit to identify and neutralize these networks.
Infrastructure Footprints
Every email sent carries a payload of technical metadata. This includes IP addresses, server headers, and routing information. In a shared pool, thousands of accounts often share a narrow range of IP addresses or utilize the same cloud hosting providers. When a spam filter sees thousands of 'different' users all communicating from the same data center subnet, it doesn't see a diverse community; it sees a botnet.
Even when pools attempt to use proxy networks or residential IPs, the 'velocity' of the mail—how many emails are sent in a specific window—often remains constant across the entire pool. This lack of variance in infrastructure usage is a massive red flag for ISPs (Internet Service Providers).
Behavioral Pattern Recognition
Spam filters today utilize advanced machine learning models trained on trillions of data points. These models are experts at 'Pattern Recognition.' Human behavior follows a power-law distribution; we send mail at irregular intervals, we have typos, we use varied sentence structures, and our reply times fluctuate based on the time of day or our personal schedules.
The 'Mechanical' Engagement Signal
In a shared inbox pool, engagement is triggered by scripts. When Account A sends an email to Account B, Account B might reply within exactly 120 seconds every single time. Or perhaps the reply always happens within a predictable 5-to-10-minute window. While this might look like engagement to a human observer, to an algorithm, it is a rhythmic, mechanical signal.
Furthermore, the content of these 'warm-up' emails is often nonsensical or repetitive. Even if AI is used to generate text, the underlying semantic patterns—the way concepts are linked—often remain static across the pool. Filters can detect this 'low-entropy' communication, marking it as non-human.
The Closed-Loop Problem
Perhaps the most significant behavioral flaw is the 'Closed-Loop' nature of shared pools. Most of these networks primarily facilitate communication between accounts within their own database. Account A talks to Account B, who talks to Account C, all of whom are members of the same service.
Real-world email networks are 'Open-Loop.' A legitimate business owner sends emails to customers, vendors, and partners across thousands of different domains and providers. When a filter observes a cluster of domains that almost exclusively interact with each other, it identifies a 'reputation silo.' These silos are easily discounted or blacklisted because they lack external validation from the broader internet ecosystem.
Technical Identifiers and Fingerprinting
Beyond behavior, there are hard technical identifiers that make shared pools easy to spot. These are often buried in the email headers or the way the SMTP (Simple Mail Transfer Protocol) handshake is performed.
Header Consistency
Email headers contain information about the mail client used to send the message (the User-Agent). Shared pools often use custom-built scripts or specific libraries to send mail. These libraries often leave unique 'fingerprints' in the headers. If a filter sees a surge of mail from a specific, obscure library that isn't a standard mail client like Outlook, Gmail, or Apple Mail, it triggers an investigation.
Tracking Pixel Anomalies
Many shared pools use tracking pixels to monitor if an email was opened. These pixels are hosted on specific domains. If thousands of accounts are all loading tracking pixels from the same small set of domains, the ISP can easily identify the common thread. By blacklisting the tracking domain, they effectively blind the pool and flag every email associated with it.
The Impact of IP and Domain Reputation Overlap
The fundamental risk of a shared pool is 'Contagion.' In a shared environment, your domain’s reputation is linked to every other domain in the pool.
The Bad Actor Effect
If one user in a shared pool uses their accounts for aggressive, 'spammy' outreach, they degrade the reputation of the entire pool. Because the pool is interconnected, the filters begin to associate the shared infrastructure and behavioral patterns with that bad actor. Even if you are following every best practice, your emails can be caught in the dragnet because you 'look' like the spammer sharing your pool.
ISPs use 'Reputation by Association.' If your domain is frequently seen interacting with a cluster of domains that have already been flagged for low-quality content, your domain will eventually be 'guilty by association.' This is why isolated, dedicated environments are far superior for high-value outreach.
Why 'Warm-up' Services Often Fail
Many shared inbox pools are marketed as 'Warm-up' services. The idea is that by sending fake emails to other accounts in the pool, you can 'trick' the ISP into thinking you are a high-volume, high-reputation sender. However, this strategy is increasingly ineffective for several reasons:
- Volume Spikes: Going from zero to 100 emails a day in a perfectly linear fashion is not how real businesses grow. Filters recognize this artificial ramp-up.
- Lack of Real Replies: Replies in a pool are often automated. They don't lead to further back-and-forth conversation, which is a key metric for 'true' engagement.
- No Organic Search/Click Activity: Real engagement involves users clicking links, searching for the sender's domain, and adding the sender to their contacts. Automated pools rarely simulate these complex side-actions effectively.
To overcome these hurdles, a more sophisticated approach is required. This is where EmaReach provides a distinct advantage. By utilizing AI that writes unique, context-aware outreach and managing the warm-up process across a multi-account architecture, it avoids the pitfalls of generic shared pools, ensuring that your communication remains indistinguishable from high-quality human activity.
The Evolution of ISP Defense Mechanisms
It is important to remember that companies like Google and Microsoft employ some of the world’s best data scientists. They are fully aware of shared inbox pools and have developed specific countermeasures to combat them.
Graph Theory and Network Analysis
ISPs use graph theory to map out relationships between domains. They can visualize the entire web of communication. In these visualizations, shared pools stick out like sore thumbs—they appear as highly dense, isolated clusters with very few 'edges' (connections) leading out to the rest of the web. Once a cluster is identified, a single 'kill switch' can effectively neutralize every domain within it.
Temporal Analysis
Filters also analyze the 'Time of Arrival.' If a group of domains all send their daily 'warm-up' batch at the same time every day, regardless of time zones or holidays, it signals a cron-job (automated script) rather than a human. Humans are inconsistent; machines are not. This temporal consistency is one of the easiest ways to detect an automated pool.
Moving Beyond Shared Pools: Best Practices for Deliverability
If shared pools are a liability, what is the alternative? The answer lies in authenticity and decentralization.
Use Dedicated IP Ranges and Domains
Instead of sharing a pool, use dedicated domains and subdomains for your outreach. This ensures that your reputation is your own. You are not at the mercy of a 'bad neighbor' who might be spamming from the same pool.
Focus on Quality Content
Automation should be a tool for efficiency, not a mask for low-quality content. Using AI to generate personalized, relevant messages is far more effective than sending thousands of generic templates. When your recipients actually want to read your mail, they engage with it naturally, providing the highest quality reputation signal possible.
Diversify Your Sending Infrastructure
Distributing your outreach across multiple accounts and providers reduces the risk of a single point of failure. If one account faces a temporary dip in reputation, your entire campaign doesn't come to a halt. This 'multi-account' strategy is a hallmark of professional-grade outreach.
Conclusion
Shared inbox pools are a relic of a simpler era of email marketing. Today, they are a 'Deliverability Debt' that will eventually come due. The transparency of these networks to modern spam filters makes them a high-risk gamble with your domain’s most valuable asset: its reputation.
From infrastructure footprints and mechanical engagement patterns to the 'closed-loop' nature of their communications, shared pools provide too many signals for ISPs to ignore. As filters continue to incorporate more advanced AI and network analysis, the detection of these pools will only become faster and more accurate.
For those who refuse to compromise on their outreach success, the path forward involves embracing tools that prioritize authenticity and technical excellence. By moving away from shared pools and toward intelligent, AI-driven systems like EmaReach, you ensure that your cold emails don't just get sent—they get delivered, read, and replied to. In the modern inbox, there is no substitute for real quality and strategic sending architecture.
EmaReach AI
Ready to scale your cold email outreach?
Join thousands of teams using EmaReach AI for AI-powered campaigns, domain warmup, and 95%+ deliverability. Start free — no credit card required.
Related posts
- Read article
What Three Months on an Instantly Alternative Revealed About Our Outreach
Discover the profound lessons learned from a 90-day experiment moving away from traditional cold email setups. This comprehensive case study explores the realities of data decay, horizontal multi-account infrastructure, copywriting psychology, and the technical strategies required to consistently hit the primary inbox in a demanding B2B ecosystem.
- Read article
Why Some Teams Return to Instantly After Trying Every Alternative
Discover why modern sales teams and agencies frequently abandon multi-channel alternatives to return to Instantly. This post explores how unlimited inbox rotation, infrastructure stability, and operational efficiency draw outbound professionals back to their core email engine.